加密测试的存储过程
IF EXISTS(SELECT 1 FROM SYSOBJECTS WHERE TYPE='P' AND NAME='P_TEST')DROP PROCEDURE P_TESTGOCREATE PROCEDURE P_TEST(@USERNAME VARCHAR(20),@MSG VARCHAR(20) OUTPUT)WITH ENCRYPTIONASBEGIN IF(SELECT COUNT(1) FROM Custs WHERE NAME=@USERNAME)>0 SET @MSG='此用户名存在' ELSE SET @MSG='此用户名不存在'END
解密的存储过程
Create PROCEDURE Decryption(@procedure sysname = NULL)ASSET NOCOUNT ONDECLARE @intProcSpace bigint, @t bigint, @maxColID smallint,@procNameLength intselect @maxColID = max(subobjid) FROMsys.sysobjvalues WHERE objid = object_id(@procedure)--select @maxColID as 'Rows in sys.sysobjvalues'select @procNameLength = datalength(@procedure) + 29DECLARE @real_01 nvarchar(max)DECLARE @fake_01 nvarchar(max)DECLARE @fake_encrypt_01 nvarchar(max)DECLARE @real_decrypt_01 nvarchar(max),@real_decrypt_01a nvarchar(max)declare @objtype varchar(2),@ParentName nvarchar(max)select @real_decrypt_01a = ''--提取对象的类型如是存储过程还是函数,如果是触发器,还要得到其父对象的名称select @objtype=type,@parentname=object_name(parent_object_id)from sys.objects where [object_id]=object_id(@procedure)-- 从sys.sysobjvalues里提出加密的imageval记录SET @real_01=(SELECT top 1 imageval FROM sys.sysobjvalues WHERE objid =object_id(@procedure) and valclass = 1 order by subobjid) --创建一个临时表create table #output ( [ident] [int] IDENTITY (1, 1) NOT NULL ,[real_decrypt] NVARCHAR(MAX) )--开始一个事务,稍后回滚BEGIN TRAN--更改原始的存储过程,用短横线替换if @objtype='P' SET @fake_01='ALTER PROCEDURE '+ @procedure +' WITH ENCRYPTION AS select 1 /**//*'+REPLICATE(cast('*'as nvarchar(max)), datalength(@real_01) /2 - @procNameLength)+'*/'else if @objtype='FN' SET @fake_01='ALTER FUNCTION '+ @procedure +'() RETURNS INT WITH ENCRYPTION AS BEGIN RETURN 1 /**//*'+REPLICATE(cast('*'as nvarchar(max)), datalength(@real_01) /2 - @procNameLength)+'*/ END'else if @objtype='V' SET @fake_01='ALTER view '+ @procedure +' WITH ENCRYPTION AS select 1 as col /**//*'+REPLICATE(cast('*'as nvarchar(max)), datalength(@real_01) /2 - @procNameLength)+'*/'else if @objtype='TR' SET @fake_01='ALTER trigger '+ @procedure +' ON '+@parentname+'WITH ENCRYPTION AFTER INSERT AS RAISERROR (''N'',16,10) /**//*'+REPLICATE(cast('*'as nvarchar(max)), datalength(@real_01) /2 - @procNameLength)+'*/'EXECUTE (@fake_01)--从sys.sysobjvalues里提出加密的假的SET @fake_encrypt_01=(SELECT top 1 imageval FROM sys.sysobjvalues WHERE objid =object_id(@procedure) and valclass = 1 order by subobjid )if @objtype='P' SET @fake_01='Create PROCEDURE '+ @procedure +' WITH ENCRYPTION AS select 1 /**//*'+REPLICATE(cast('*'as nvarchar(max)), datalength(@real_01) /2 - @procNameLength)+'*/'else if @objtype='FN' SET @fake_01='CREATE FUNCTION '+ @procedure +'() RETURNS INT WITH ENCRYPTION AS BEGIN RETURN 1 /**//*'+REPLICATE(cast('*'as nvarchar(max)), datalength(@real_01) /2 - @procNameLength)+'*/ END'else if @objtype='V' SET @fake_01='Create view '+ @procedure +' WITH ENCRYPTION AS select 1 as col /**//*'+REPLICATE(cast('*'as nvarchar(max)), datalength(@real_01) /2 - @procNameLength)+'*/'else if @objtype='TR' SET @fake_01='Create trigger '+ @procedure +' ON '+@parentname+'WITH ENCRYPTION AFTER INSERT AS RAISERROR (''N'',16,10) /**//*'+REPLICATE(cast('*'as nvarchar(max)), datalength(@real_01) /2 - @procNameLength)+'*/'--开始计数SET @intProcSpace=1--使用字符填充临时变量SET @real_decrypt_01 = replicate(cast('A'as nvarchar(max)), (datalength(@real_01) /2 ))--循环设置每一个变量,创建真正的变量--每次一个字节SET @intProcSpace=1--如有必要,遍历每个@real_xx变量并解密WHILE @intProcSpace<=(datalength(@real_01)/2)BEGIN--真的和假的和加密的假的进行异或处理SET @real_decrypt_01 = stuff(@real_decrypt_01, @intProcSpace, 1,NCHAR(UNICODE(substring(@real_01, @intProcSpace, 1)) ^(UNICODE(substring(@fake_01, @intProcSpace, 1)) ^UNICODE(substring(@fake_encrypt_01, @intProcSpace, 1)))))SET @intProcSpace=@intProcSpace+1END --通过sp_helptext逻辑向表#output里插入变量insert #output (real_decrypt) select @real_decrypt_01--select real_decrypt AS '#output chek' from #output --测试-- ---------------------------------------开始从sp_helptext提取-- -------------------------------------declare @dbname sysname,@BlankSpaceAdded int,@BasePos int,@CurrentPos int,@TextLength int,@LineId int,@AddOnLen int,@LFCR int --回车换行的长度,@DefinedLength int,@SyscomText nvarchar(max),@Line nvarchar(255)Select @DefinedLength = 255SELECT @BlankSpaceAdded = 0 --跟踪行结束的空格。注意Len函数忽略了多余的空格CREATE TABLE #CommentText(LineId int,Text nvarchar(255) collate database_default)--使用#output代替sys.sysobjvaluesDECLARE ms_crs_syscom CURSOR LOCALFOR SELECT real_decrypt from #outputORDER BY identFOR READ ONLY--获取文本SELECT @LFCR = 2SELECT @LineId = 1OPEN ms_crs_syscomFETCH NEXT FROM ms_crs_syscom into @SyscomTextWHILE @@fetch_status >= 0BEGINSELECT @BasePos = 1SELECT @CurrentPos = 1SELECT @TextLength = LEN(@SyscomText)WHILE @CurrentPos != 0BEGIN--通过回车查找行的结束SELECT @CurrentPos = CHARINDEX(char(13)+char(10), @SyscomText,@BasePos)--如果找到回车IF @CurrentPos != 0BEGIN--如果@Lines的长度的新值比设置的大就插入@Lines目前的内容并继续While (isnull(LEN(@Line),0) + @BlankSpaceAdded +@CurrentPos-@BasePos + @LFCR) > @DefinedLengthBEGINSELECT @AddOnLen = @DefinedLength-(isnull(LEN(@Line),0) +@BlankSpaceAdded)INSERT #CommentText VALUES( @LineId,isnull(@Line, N'') + isnull(SUBSTRING(@SyscomText,@BasePos, @AddOnLen), N''))SELECT @Line = NULL, @LineId = @LineId + 1,@BasePos = @BasePos + @AddOnLen, @BlankSpaceAdded = 0ENDSELECT @Line = isnull(@Line, N'') +isnull(SUBSTRING(@SyscomText, @BasePos, @CurrentPos-@BasePos + @LFCR), N'')SELECT @BasePos = @CurrentPos+2INSERT #CommentText VALUES( @LineId, @Line )SELECT @LineId = @LineId + 1SELECT @Line = NULLENDELSE--如果回车没找到BEGINIF @BasePos <= @TextLengthBEGIN--如果@Lines长度的新值大于定义的长度While (isnull(LEN(@Line),0) + @BlankSpaceAdded +@TextLength-@BasePos+1 ) > @DefinedLengthBEGINSELECT @AddOnLen = @DefinedLength -(isnull(LEN(@Line),0) + @BlankSpaceAdded)INSERT #CommentText VALUES( @LineId,isnull(@Line, N'') + isnull(SUBSTRING(@SyscomText,@BasePos, @AddOnLen), N''))SELECT @Line = NULL, @LineId = @LineId + 1,@BasePos = @BasePos + @AddOnLen, @BlankSpaceAdded =0ENDSELECT @Line = isnull(@Line, N'') +isnull(SUBSTRING(@SyscomText, @BasePos, @TextLength-@BasePos+1 ), N'')if LEN(@Line) < @DefinedLength and charindex(' ',@SyscomText, @TextLength+1 ) > 0BEGINSELECT @Line = @Line + ' ', @BlankSpaceAdded = 1ENDENDENDENDFETCH NEXT FROM ms_crs_syscom into @SyscomTextENDIF @Line is NOT NULLINSERT #CommentText VALUES( @LineId, @Line )select Text from #CommentText order by LineIdCLOSE ms_crs_syscomDEALLOCATE ms_crs_syscomDROP TABLE #CommentText-- ---------------------------------------结束从sp_helptext提取-- ---------------------------------------删除用短横线创建的存储过程并重建原始的存储过程ROLLBACK TRANDROP TABLE #outputGO启用DACSP_CONFIGURE 'remote admin connections';GO----0:仅允许本地连接使用 DAC,1:允许远程连接使用 DACSP_CONFIGURE 'remote admin connections', 0;GORECONFIGURE WITH OVERRIDE;GO 文件――>新建――>数据库引擎查询
服务器名称:admin:.或者admin:服务器名称
登录进去执行解密操作
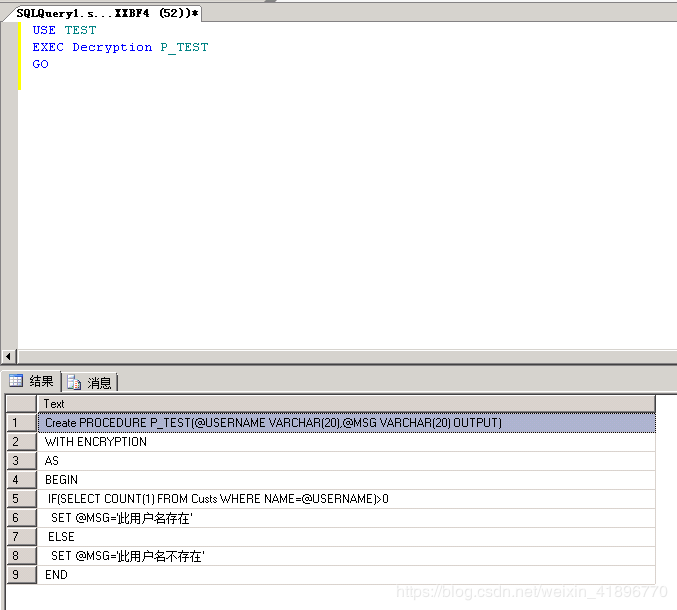
USE TESTEXEC Decryption P_TESTGO
为了安全起见,不要在正式环境进行解密,避免在解密过程中将原存储过程损坏!
总结
以上所述是小编给大家介绍的SQLSERVER对加密的存储过程、视图、触发器进行解密,希望对大家有所帮助,如果大家有任何疑问请给我留言,小编会及时回复大家的。在此也非常感谢大家对武林网网站的支持!
如果你觉得本文对你有帮助,欢迎转载,烦请注明出处,谢谢!
新闻热点
疑难解答